JetBrains debuts Amazing AI model in the software industry
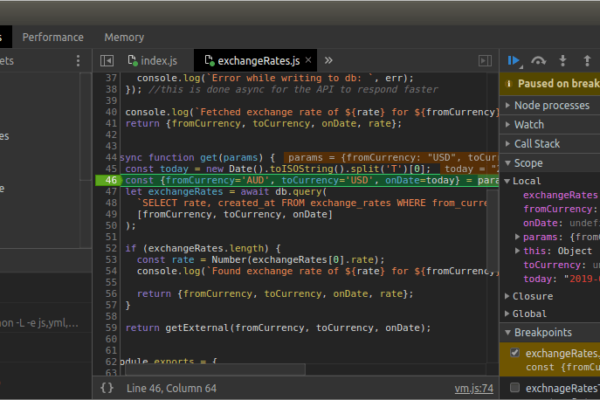
JetBrains has introduced Mellum, its proprietary AI model tailored for software development tasks. Mellum is exclusively integrated into JetBrains’ AI Assistant, delivering significant enhancements in both the speed and accuracy of code completions compared to earlier versions. In contrast to larger language models, Mellum is designed with a smaller footprint to provide near-instant coding suggestions….