Hacking
Here is How robotics can be used to better understand the ‘sense of self’ in humans
In a recent review published in Science Robotics, a cognitive roboticist, cognitive psychologist, and psychiatrist explore the fascinating concept of “sense of self” in humans and how robots could offer new insights into this phenomenon. The experience of being a self—connected to our bodies and capable of interacting with the world—feels natural to us as…

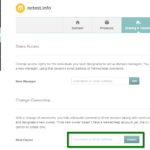
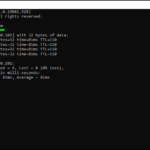
Here are amazing tips on basic Hacking Techniques
Phishing is a tactic used by cybercriminals to steal sensitive information, such as passwords or credit card details, by posing as a trustworthy source. They trick individuals into clicking on links that lead to fake websites designed to capture their data. These attacks often create a sense of urgency—claiming there’s a security issue or a…

India’s court in a standstill | crypto hackers
The official YouTube channel of the Supreme Court of India, which was used for streaming proceedings, was reportedly hacked on Friday and displayed cryptocurrency advertisements. Videos related to a cryptocurrency product were uploaded to the channel, but the entire page has since been removed. The Supreme Court had been using the platform to live broadcast…



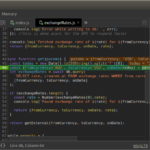
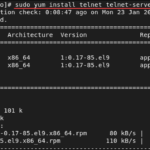
Top Ethical Hacking Tools in the year 2023
Invicti Is a web application security scanner hacking tool to find SQL Injection, XSS, and vulnerabilities in web applications or services automatically. It is usually available on SAAS solution Features:It detects Dead accurate vulnerability with the help of unique Proof-Based Scanning Technology.It requires minimal configuration with a scalable solution. It automatically detects URL rewrite rules…

Ethical hacking in the realm of security
The landscape of ethical hacking and penetration testing has transformed significantly due to the emergence of automated tools. Presently, numerous tools are under development that can expedite the testing process. Ethical hacking plays a crucial role in assisting organizations to enhance the protection of their information and systems. Additionally, it serves as one of the…

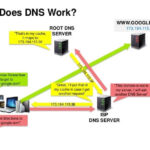
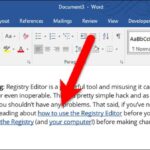
Hacking in the context of IT
Hacking refers to the act of gaining unauthorized access to computer systems or networks for various purposes, including testing security, identifying vulnerabilities, or committing cybercrimes. Here are some notes on the advantages and disadvantages of hacking: Advantages of Hacking: Disadvantages of Hacking: It is essential to differentiate between ethical hacking, which aims to improve cybersecurity,…