Ethical hacking in the realm of security
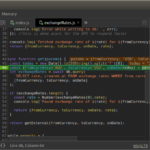
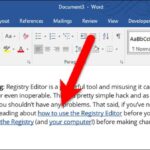
The landscape of ethical hacking and penetration testing has transformed significantly due to the emergence of automated tools. Presently, numerous tools are under development that can expedite the testing process. Ethical hacking plays a crucial role in assisting organizations to enhance the protection of their information and systems. Additionally, it serves as one of the…